bitcoin escrow script

Simple A bitcoin escrow process you can go through in 3 quick and easy steps.Its so simple you will wonder why you have never heard of us before.Affordable We charge a small flat escrow fee of 1 percent on all escrow transactions.We even offer you the ability to split the fee with the other party.Quick You can create an escrow transaction in minutes and view the status instantly.We strive to respond to support requests as soon as possible Secure We keep your funds as secure as possible either being stored with Coinapult for transactions fixed to a fiat value, or in cold storage.Regular Escrow You deposit your funds into a bitcoin address controlled by us and the funds are forwarded to cold storage Regular Escrow pegged to fiat value You deposit into a bitcoin address controlled by Coinapult and Coinapult pegs the value to a fiat or asset value Mutli-Signature Escrow Your funds are kept in a secure 2 of 3 multi-signature transaction where we hold only one key Multi-Signature Escrow pegged to a fiat value Your funds are kept in a secure 2 of 3 multi-signature transaction using Omni(mastercoin) or Nubits to peg the value

Jump to: , A distributed contract is a method of using Bitcoin to form agreements with people via the block chain.Contracts don't make anything possible that was previously impossible, but rather, they allow you to solve common problems in a way that minimizes trust.Minimal trust often makes things more convenient by allowing human judgements to be taken out of the loop, thus allowing complete automation.By building low trust protocols that interact with Bitcoin, entirely new products can be created: This page also lists some smaller examples.Many of the ideas underlying Bitcoin contracts were first described by Nick Szabó in his seminal paper, Formalizing and Securing Relationships on Public Networks.These pages were written by Mike Hearn.Contact him if you have an idea for a new type of contract.You can watch a video of a talk on contracts that was presented at the Bitcoin 2012 conference in London.Contents 1 2 3 4 5 6 7 8 9 In places this page refers to the ability to use the nSequence field for transaction mempool replacement.

This mechanism was disabled in 2010, and more recently the code has been removed completely, due to concerns over people using it to perform DoS attacks.Implementors should take this into account and try to create contract mechanisms that do not rely on mempool replacement if they wish to have their implementations work with current implementations.If Bitcoin changes in future to allow mempool replacement once again, this page will be updated.
bitcoin sistemi nedirEvery transaction in Bitcoin has one or more inputs and outputs.
bitcoin idr chartEach input/output has a small, pure function associated with it called a script.
litecoin mining 2 different cardsScripts can contain signatures over simplified forms of the transaction itself.
bitcoin core wallet review
Every transaction can have a lock time associated with it.This allows the transaction to be pending and replaceable until an agreed-upon future time, specified either as a block index or as a timestamp (the same field is used for both, but values less than 500 million are interpreted as a block index).If a transaction's lock time has been reached, we say it is final.
asic in litecoinEach transaction input has a sequence number.
galaxy s5 bitcoinIn a normal transaction that just moves value around, the sequence numbers are all UINT_MAX and the lock time is zero.
bitcoin ticker htmlIf the lock time has not yet been reached, but all the sequence numbers are UINT_MAX, the transaction is also considered final.
bitcoin theft australia
Sequence numbers can be used to issue new versions of a transaction without invalidating other inputs signatures, e.g., in the case where each input on a transaction comes from a different party, each input may start with a sequence number of zero, and those numbers can be incremented independently.Signature checking is flexible because the form of transaction that is signed can be controlled through the use of SIGHASH flags, which are stuck on the end of a signature.
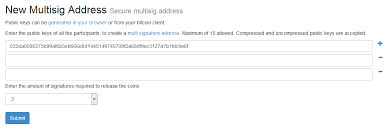
bitcoin iqoptionIn this way, contracts can be constructed in which each party signs only a part of it, allowing other parts to be changed without their involvement.The SIGHASH flags have two parts, a mode and the ANYONECANPAY modifier: The SIGHASH_ANYONECANPAY modifier can be combined with the above three modes.When set, only that input is signed and the other inputs can be anything.Scripts can contain the CHECKMULTISIG opcode.This opcode provides n-of-m checking: you provide multiple public keys, and specify the number of valid signatures that must be present.

The number of signatures can be less than the number of public keys.An output can require two signatures to be spent by setting it to something like this: There are two general patterns for safely creating contracts: This is to ensure that people always know what they are agreeing to.Together, these features let us build interesting new financial tools on top of the block chain.Imagine that you open an account on a website (eg, a forum or wiki) and wish to establish your trustworthiness with the operators, but you don't have any pre-existing reputation to leverage.One solution is to buy trust by paying the website some money.But if at some point you close your account, you'd probably like that money back.You may not trust the site enough to give them a deposit that they are tempted to spend.Another risk is that the site might just disappear one day.The goal is to prove that you made a sacrifice of some kind so the site knows you're not a spambot, but you don't want them to be able to spend the money.

And if the operators disappear, you'd eventually like the coins back without needing anything from them.We can solve this problem with a contract: At this stage, the 10 BTC are in a state where neither the user nor the website can spend them independently.After six months, the contract will complete and the user will get the coins back, even if the website disappears.What if the user wishes to close his account early?The website creates a new version of Tx2 with nLockTime set to zero and the input sequence number set to UINT_MAX, then he re-signs it.The site hands the tx back to the user, who signs it as well.The user then broadcasts the transaction, terminating the contract early and releasing the coins.What if the six months is nearly up and the user wishes to keep his account?The same thing applies: the contract can be resigned with a newer nLockTime, a sequence number 1 higher than the previous and rebroadcast 2^32 times.No matter what happens, both parties must agree for the contract to change.

Obviously, if the user turns out to be abusive (i.e., a spammer), the website will not allow an early close of the contract.If too much abuse is getting through, the size of the deposit can be raised or the length of the contract can be increased.A buyer wants to trade with somebody he doesn't know or trust.In the common case where the transaction goes well, the client doesn't want any third parties involved.If something goes wrong though, he'd like a third party to decide who gets the money - perhaps a professional dispute mediation service.Note that this concept can apply to either buyer or seller.The mediator might request proof of postage from the merchant, for example.In other words, one wants to lock up some coins so a third party has to agree in order for them to be spent: Now the coins are locked in such a way that they can only be spent by the following methods: When signing an input, the contents are set to the connected output.Thus, to redeem this transaction, the client creates a scriptSig containing zeros where the other signature should be, signs it, and then sets one of the slots to his new signature.

The partially-complete transaction can then be sent to the merchant or mediator for the second signature.An assurance contract is a way of funding the creation of a public good, that is, a good that, once created, anyone can benefit from for free.The standard example is a lighthouse: whilst everyone may agree that one should be built, it’s too expensive for an individual sailor to justify building one, given that it will also benefit all his competitors.One solution is for everyone to pledge money towards the creation of the public good, such that the pledges are only committed if the total value of all pledges is above the cost of creation.If not enough people contribute, nobody has to pay anything.Examples where Bitcoin is superior to traditional payment methods for assurance contract fundraising include applications where frequent, small pledges need to be made automatically, for instance internet radio station funding and web page translation.Consider a browser extension that you send a bit of money to.

It detects the current language of the page and broadcasts a pledge for a translation into your language to be prepared.If enough users with the extension land on the same page at the same time (eg, it was linked to from somewhere high traffic), then enough pledges are broadcast to trigger a payment to a company who prepares a high quality translation.When complete it automatically loads in your browser.We can model this in Bitcoin as follows: This scheme relies on several aspects of the protocol.The first is the SIGHASH flags used.SIGHASH_ALL is the default and means the entire contents of the transaction are signed, except for the input scripts.SIGHASH_ANYONECANPAY is an additional modifier that means the signature only covers the input it’s found in - the other inputs are not signed and thus can be anything.By combining these flags together, we are able to create a signature that is valid even when other inputs are added, but breaks if the outputs or other properties of the transaction are changed.

The second aspect we exploit is the fact that a transaction in which the output values are larger than the input values is invalid (for obvious reasons).This means it’s safe to send the entrepreneur a transaction that spends such coins - it’s impossible for him to claim the coins unless he has other inputs that sum to the output value or more.It's possible to create assurance contracts without using SIGHASH_ANYONECANPAY.Instead, a two step process is used in which pledges are collected without transactions, and once the total value is reached, a transaction with an input for each pledger is created and passed around until all signatures are collected.However, using SIGHASH_ANYONECANPAY and then merging is probably more convenient.An assurance contract can be prepared for funding network security for the next block.In this way, mining can be funded even if block space is not scarce.An elaboration of this concept is described by Tabarrok in his paper, “The private provision of public goods via dominant assurance contracts”.

In a dominant assurance contract, if a contract fails (not enough pledges within a set time window) the entrepreneur pays a fee to those who pledged so far.This type of contract attempts to arrange incentives such that taking part is always the right strategy.A scheme for dominant assurance contracts in Bitcoin has been proposed.Scripts are, by design, pure functions.They cannot poll external servers or import any state that may change as it would allow an attacker to outrun the block chain.What's more, the scripting language is extremely limited in what it can do.Fortunately, we can make transactions connected to the world in other ways.Consider the example of an old man who wishes to give an inheritance to his grandson, either on the grandson's 18th birthday or when the man dies, whichever comes first.To solve this, the man first sends the amount of the inheritance to himself so there is a single output of the right amount.Then he creates a transaction with a lock time of the grandson's 18th birthday that pays the coins to another key owned by the grandson, signs it, and gives it to him - but does not broadcast it.

This takes care of the 18th birthday condition.If the date passes, the grandson broadcasts the transaction and claims the coins.He could do it before then, but it doesn't let him get the coins any earlier, and some nodes may choose to drop transactions in the memory pool with lock times far in the future.The death condition is harder.As Bitcoin nodes cannot measure arbitrary conditions, we must rely on an oracle.An oracle is a server that has a keypair, and signs transactions on request when a user-provided expression evaluates to true.Here is an example.The man creates a transaction spending his output, and sets the output to: This is the oracle script.It has an unusual form - it pushes data to the stack then immediately deletes it again.The pubkey is published on the oracle's website and is well-known.The hash is set to be the hash of the user-provided expression stating that he has died, written in a form the oracle knows how to evaluate.For example, it could be the hash of the string: This little language is hypothetical, it'd be defined by the oracle and could be anything.

The return value is an output: an amount of value and an address owned by the grandson.Once more, the man creates this transaction but gives it directly to his grandson instead of broadcasting it.He also provides the expression that is hashed into the transaction and the name of the oracle that can unlock it.It is used in the following algorithm: If, and only if, the oracle agrees that the man is dead, the grandson can broadcast the two transactions (the contract and the claim) and take the coins.Oracles can potentially evaluate anything, yet the output script form in the block chain can always be the same.Consider the following possibilities: The conditions that control whether the oracle signs can be arbitrarily complex, but the block chain never needs to contain more than a single hash.The Early Temple project has implemented a prototype of an oracle that looks for a key phrase in a web page.There are various ways to reduce the level of required trust in the oracle.Going back to our first example, the oracle has not seen the transaction the grandson is trying to unlock, as it was never broadcast, thus, it cannot hold the grandson to ransom because it does not know whether the transaction it's signing for even exists.
People can, and should, regularly challenge the oracle in an automated fashion to ensure it always outputs what is expected.The challenges can be done without spending any coins because the tx to be signed can be invalid (ie, connected to transactions that don't exist).The oracle has no way to know whether a request to be signed is random or real.How to challenge the oracle with conditions that are not yet true is however an open research question.The number of keys in the CHECKMULTISIG can be increased to allow for n-of-m oracles if need be.Of course, it is vital to check that the oracles really are independent and not in collusion.An implementation of such a system, and explanation was published in the Orisi whitepaper.The idea, in short, is that independent oracles could be run by a set of trustworthy independent actors.Contract participants would first settle upon a set of oracles they both are comfortable using - for example by trusting a dedicated site - and then sign a contract requiring most of the oracles signatures to resolve.

One of the interesting properties of such a system is that it can possibly implement very complicated sets of scripts and external inputs, while being based on a set of standard bitcoin scripts.Another property is that the oracles can possibly replace each ones by forwarding the funds to new multisig addresses when they discover that one of the oracles is faulty/corrupted.Finally, such oracles could be used to implement sidechains without dedicated blockchain opcodes.Using commodity hardware, you can use trusted computing in the form of Intel TXT or the AMD equivalent (SKINIT) to set up a sealed hardware environment and then use the TPM chip to attest that fact to a third party.That third party can verify the hardware was in the required state.Defeating this requires someone to be able to interfere with the execution of a program that may run entirely on the CPU, even in extreme cases without any data traversing the memory bus (you can run entirely using on-die cache if the program is small enough).

Finally, perhaps the most practical approach currently is to use Amazon Web Services.As of November 2013, the closest we have to a working oracle is this recipe for creating a trusted computing environment using AWS, built in support of this project for doing selective SSL logging and decryption.The idea is that an oracle, which can be proven trustworthy using the Amazon APIs with Amazon as the root of trust, records encrypted SSL sessions to an online banking interface in such a way that later if there is a dispute about a person-to-person exchange, the logs can be decrypted and the dispute settled.The Bitcoin technology can be adapted to create multiple, independent currencies.NameCoin is an example of one such currency that operates under a slightly different set of rules, and can also be used to rent names in a namespace.Currencies that implement the same ideas as Bitcoin can be traded freely against each other with limited trust.For example, imagine a consortium of companies that issue EURcoins, a crypto-currency that is backed 1:1 by deposits in the consortium's bank accounts.

Such a currency would have a different set of tradeoffs to Bitcoin: more centralized, but without FX risk.People might wish to trade Bitcoins for EURcoins back and forth, with the companies only getting involved when cashing in/out of the regular banking system.To implement this, a protocol proposed by TierNolan can be used: This protocol makes it feasible to do trades automatically in an entirely peer-to-peer manner, which should ensure good liquidity.The chain-trade script could look like this: The contract input script looks like either: i.e., the first data element selects which phase is being used.See Atomic cross-chain trading for details.Note that whilst EURcoins is a natural idea, there are other ways to implement peer-to-peer currency exchange (Bitcoin to fiat and vice versa), see the Ripple currency exchange article for more information.Sergio Demian-Lerner proposed P2PTradeX, a solution requiring the validation rules for one blockchain to be effectively encoded into the validation rules for the other.

In example 4, we saw how to make payments conditional on the output of some arbitrary program.Those programs are very powerful and can do anything a regular program can do, like fetching web pages.The downside is that a third party is required (an oracle).Although there are techniques that can help reduce the trust needed in the oracle, none can reduce it to zero.For a restricted class of programs, pure functions, new cryptographic techniques are starting to become available that can actually reduce the trust needed all the way to zero with no third parties.These programs cannot perform any I/O, but in many cases this restriction turns out to be unimportant or can be worked around in other ways, like by giving the program a signed/timestamped document as an input instead of having the program download it.Gregory Maxwell has invented a protocol for doing this, which you can read about here: Zero Knowledge Contingent Payment Bitcoin transactions are very cheap relative to traditional payment systems, but still have a cost due to the need for it to be mined and stored.

There are some cases in which you want to rapidly and cheaply adjust the amount of money sent to a particular recipient without incurring the cost of a broadcast transaction.For example, consider an untrusted internet access point, like a WiFi hotspot in a cafe you never visited before.You'd like to pay 0.001 BTC per 10 kilobytes of usage, without opening an account with the cafe.A zero-trust solution means it could be fully automatic, so you could just pre-allocate a budget on your phone's mobile wallet at the start of the month, and then your device automatically negotiates and pays for internet access on demand.The cafe also wants to allow anyone to pay them without the fear of being ripped off.To do this, the following protocol can be used.This protocol relies upon a different behavior of nLockTime to the original design.Starting around 2013 time-locked transactions were made non standard and no longer enter the memory pool, thus cannot be broadcast before the timelock expires.When the behaviour of nLockTime is restored to the original design from Satoshi, a variant of this protocol is required which is discussed below.

We define the client to be the party sending value, and the server to be the party receiving it.This is written from the clients perspective.This continues until the session ends, or the 1-day period is getting close to expiry.The AP then signs and broadcasts the last transaction it saw, allocating the final amount to itself.The refund transaction is needed to handle the case where the server disappears or halts at any point, leaving the allocated value in limbo.If this happens then once the time lock has expired the client can broadcast the refund transaction and get back all the money.This protocol has been implemented in bitcoinj.The lock time and sequence numbers avoid an attack in which the AP provides connectivity, and then the user double-spends the output back to themselves using the first version of TX2, thus preventing the cafe from claiming the bill.If the user does try this, the TX won't be included right away, giving the access point a window of time in which it can observe the TX broadcast, and then broadcast the last version it saw, overriding the user's attempted double-spend.